GUID vs UUID: Terminology and Historical Background
The terms originate from different ecosystems.
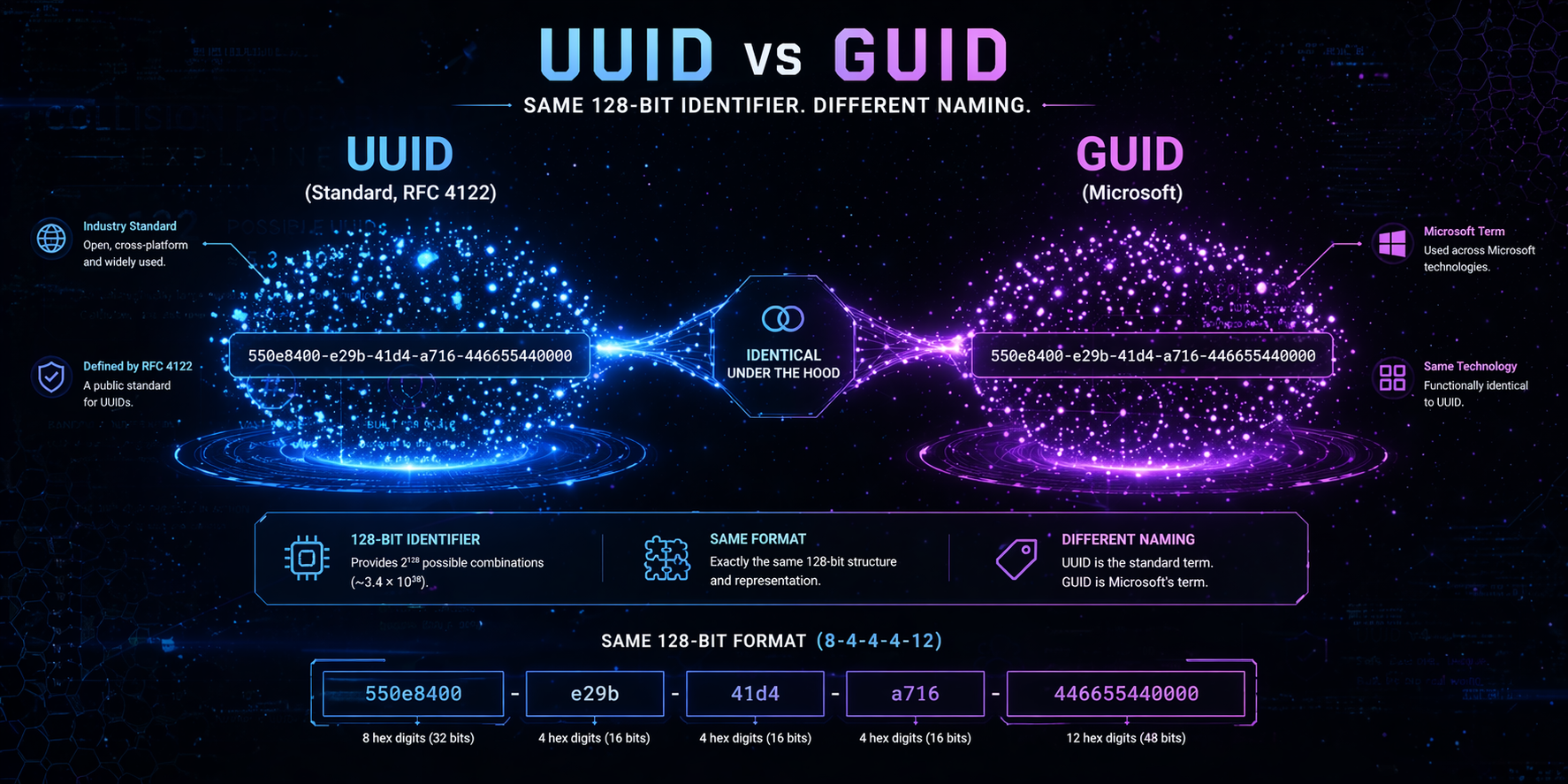
- UUID (Universally Unique Identifier) is defined by international standards such as RFC 4122 and ISO/IEC 9834-8.
- GUID (Globally Unique Identifier) is the name Microsoft uses for the same 128-bit identifier format in Windows, COM, and .NET.
RFC 4122 explicitly states that UUIDs are also known as GUIDs. Microsoft documentation confirms its identifiers follow the same structure and generation rules.
From a standards perspective, there is no structural divergence — the difference is naming convention and ecosystem context.
UUID and GUID: Internal Structure and Format
Both identifiers share identical core characteristics:
- 128 bits (16 bytes)
- Represented as 32 hexadecimal digits
- Common textual format: 8-4-4-4-12
Example:
550e8400-e29b-41d4-a716-446655440000
Structural Fields
A standardized identifier includes:
- Time-based or random component
- Version field
- Variant field
- Additional node or random bits
The version field determines how the value was generated.
The variant field determines compatibility with the specification family.
These elements exist regardless of terminology.
Difference Between GUID and UUID at the Specification Level
To evaluate the difference between GUID and UUID, we must examine specification alignment.
RFC 4122 defines:
- Bit layout
- Version numbering
- Variant encoding
- Canonical textual representation
Microsoft’s implementation aligns with these rules. Earlier Windows systems included compatibility variants, but modern GUID generation complies with RFC requirements.
Versions Defined by RFC 4122
|
Version |
Generation Method |
Typical Usage |
|
1 |
Timestamp + MAC |
Legacy systems |
|
2 |
DCE security |
Rare |
|
3 |
Name-based (MD5) |
Deterministic IDs |
|
4 |
Random |
Most common |
|
5 |
Name-based (SHA-1) |
Deterministic (stronger hash) |
In modern software, version 4 dominates due to simplicity and strong randomness.
There is no version exclusive to one term.
GUID or UUID: Practical Differences in Programming
In application development, the distinction usually appears only in API naming.
.NET
Guid id=Guid.NewGuid();
Java
UUID id=UUID.randomUUID();
Python
import uuid
uuid.uuid4()
Go
import "github.com/google/uuid"
id := uuid.New()
All examples produce RFC-compliant version 4 identifiers.
The difference lies in the type name, not in structure or generation logic.
Byte Order and Binary Representation
The most technical nuance appears at the binary level.
RFC defines fields in network byte order (big-endian).
Windows historically stored certain components internally using mixed endianness.
This affects:
- Raw byte comparisons
- Binary serialization
- Cross-platform binary exchange
Important:
The canonical textual form remains identical across platforms.
Practical Recommendation
When interoperability matters:
- Exchange identifiers as strings
- Avoid direct raw-byte comparison between systems
- Use official parsing libraries
Structural Comparison
|
Aspect |
UUID (Standard Term) |
GUID (Microsoft Term) |
|
Length |
128 bits |
128 bits |
|
Governing Spec |
RFC 4122 |
RFC-based implementation |
|
Text Format |
8-4-4-4-12 hex |
Same |
|
Common Version |
v4 |
v4 |
|
Cross-Platform |
Yes |
Yes |
|
Ecosystem Origin |
IETF / ISO |
Microsoft |
The table shows practical equivalence.
When the Distinction Actually Matters
In typical scenarios — REST APIs, microservices, databases — there is no behavioral difference.
However, care is required in:
- COM interoperability
- Legacy Windows RPC
- Low-level binary storage
- Byte-level hashing or digital signing
- Custom serialization formats
If identifiers are treated purely as 16-byte arrays, endianness must be handled explicitly.
Security and Best Practices
Security characteristics depend on version, not terminology.
- Version 1 may expose timestamp and hardware information.
- Version 4 is recommended for general-purpose unique identifiers.
- Versions 3 and 5 provide deterministic values based on names.
Best practices:
- Always use standard libraries.
- Prefer version 4 unless deterministic behavior is required.
- Store in canonical textual format for portability.
- Avoid manually constructing random 16-byte sequences — version and variant bits must be set correctly.
Final Clarification
In modern software engineering, both terms refer to the same 128-bit unique identifier standard.
The distinction is historical and ecosystem-driven:
- One term originates from formal international specifications.
- The other originates from Microsoft’s implementation naming.
Functionally, structurally, and algorithmically, they describe the same identifier format. Understanding this eliminates unnecessary confusion and shifts focus to the real engineering considerations: generation method, serialization, storage strategy, and interoperability.